Pipeline-Native
Application Security
Fully Automated from Development to Production
Software security challenges are increasing
Vulnerabilities arise both in development and in production

Software developers have to contend with backdoors in “trusted” software, the targeting of the weakest links (including external connections from suppliers and partners), and 3rd party code. And, since core systems are difficult and expensive to remediate, the risks to revenue and costs of security are growing.
Prismo helps developers with our fully automated end-to-end approach to:
- Ensure security from the start
- Systematically remediate vulnerabilities, even in a production environment
DevSecOps is finally a reality with Prismo
Secure Your Code from the Start
and Protect it in Production
Prismo automates security functions across the SDLC from development to deployment, securing custom developed code, ensuring the integrity of the software supply chain, and providing run-time protection for apps in production.
- Secures Custom Apps and APIs: Supports full-cycle DevSecOps with automated discovery and testing
- Protects VM and Container Builds: Runtime protection includes intent-based policies to protect against backdoors and real-time mitigation for active threats
- Certifies and verifies supply chain software: 3rd party and Open-Source code are tested in a cloud-native sandbox to uncover backdoors and vulnerabilities and intent-based policies provide protection

One Platform to Secure the SDLC
Comprehensive, automated, and risk-based application security and vulnerability management
 Application and API Security
Pinpoint vulnerabilities in custom applications and APIs across on-premises, Private Cloud, Public Cloud, and SaaS deployments
Application and API Security
Pinpoint vulnerabilities in custom applications and APIs across on-premises, Private Cloud, Public Cloud, and SaaS deployments
 Supply Chain Software Certification
Supply Chain Software Certification
Fingerprint and certify 3rd party and open-source software and then programmatically verify in production
 Runtime Attack Protection
Runtime Attack Protection
Monitor and protect workloads in production from new and zero-day vulnerabilities and real time attacks only seen in production
 End-to-End Pipeline Automation
Automate security across the SDLC streamlining the development process, increasing release velocity and quality, and reducing MTTRw
End-to-End Pipeline Automation
Automate security across the SDLC streamlining the development process, increasing release velocity and quality, and reducing MTTRw
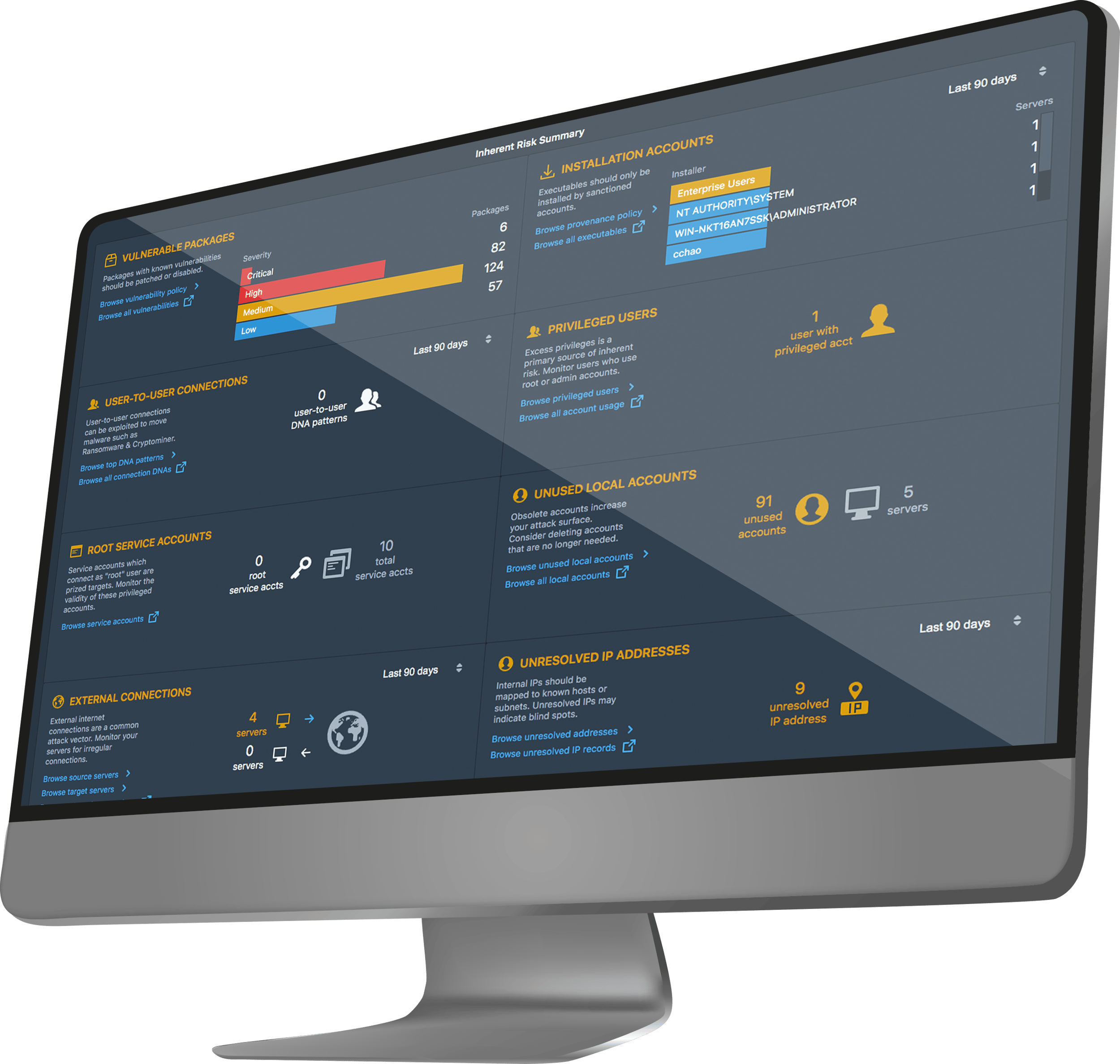
Comprehensive solution for automated and risk-based identification, prioritization, remediation, and protection for residual risk
 Continuous Compliance
Continuous Compliance
Assure compliance with out-of-the-box reports and dashboards for NIST, CIS, OWASP, MITRE, and other frameworks
Secure Application and API Code
Detect and remediate vulnerabilities across development, testing, and production
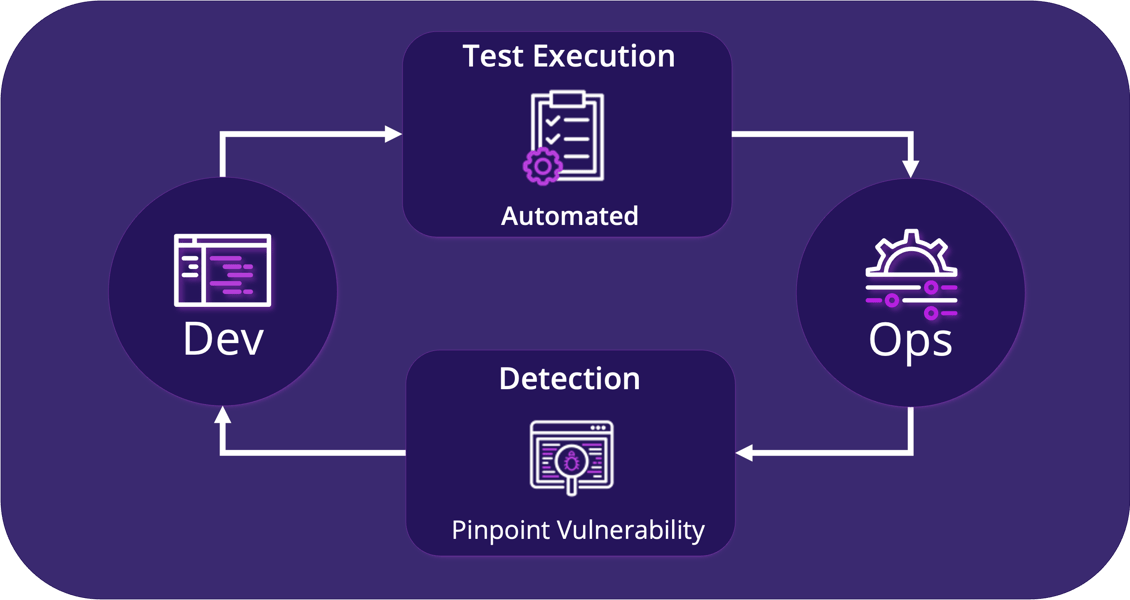
Pipeline-Native Application Scanning
As enterprises adopt Agile and DevOps methodologies to support the development of production applications, legacy security and compliance solutions become an inhibitor to rapid development and innovation. Prismo Dev-Native Security solves this challenge by automating security functions:
- Discovers incremental Build-over-Build code paths and tags them with version, build, and regression run
- Automates generation and execution of security tests with no manual intervention
- Minimizes MTTR through precise pinpointing of vulnerabilities for developers
- Mitigates residual risk in production while a vulnerability is being remediated
Secure the Supply Chain
Automatically ensure the integrity of supply chain software
Open-Source and commercial software are susceptible to backdoors and vulnerabilities making the enterprise vulnerable to supply chain and ransomware attacks. Prismo ensures the integrity of the software supply chain by:
- Automatically building an execution profile of images that includes 3rd party applications, open source and OS
- Extracting the security fingerprint and certifying the image against industry standard frameworks ( CIS, MITRE, and NIST)
- Programmatically verifying the certified fingerprint is consistent between upgrades, patches, and in production
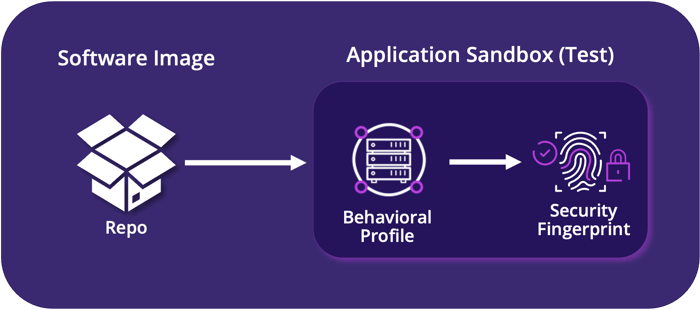
Prismo Supply Chain Software Workflow
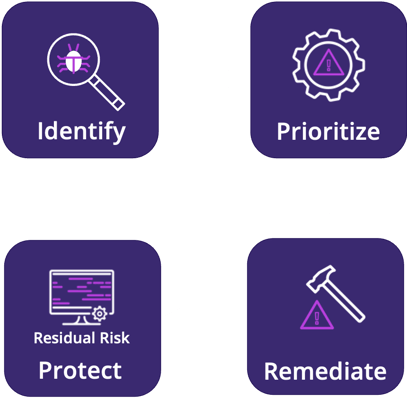
Automate Vulnerability
Lifecycle Management
Prioritize and manage residual risk using enterprise context
- Identify vulnerabilities precisely and comprehensively with continuous “Build-over-Build” identification of new code paths for speed, precision, and coverage
- Prioritize remediation resources based on risk to the business with the use of runtime and environmental context
- Continuously protect in production with automated "Protect until Patched" policies and real-time attack detection and mitigation to protect code in production
Dev-Native Security Benefits
Prismo enables your developers to take informed action and save money
Weaves security and compliance into the fabric of the SDLC, shifting security left to identify and remediate vulnerabilities early and enabling the automation of manual processes, resulting in less human effort and errors, higher quality releases, and faster release and innovation cycles.
Provides continuous enterprise-wide visibility of risk, enabling prioritization of vulnerabilities and threats, automated real-time response and continuous policy compliance, enforcement, and reporting
Enables a cyber resilient approach to security with proactive early detection and mitigation of active threats, minimization of MTTR for vulnerabilities, and reduction of RPO and RTO by detecting and stopping ransomware and supply chain attacks early to avoid and minimize operational disruption and business impact
Prismo’s unified end-to-end approach and architecture enables significant reductions in total cost of ownership through Early Identification and remediation of vulnerabilities, Automation of manual processes, Consolidation of the security stack
